danniel-lara escreveu:
tem como postar todo o seu squid.conf ?
Tem sim
é essa é a conf
#
# Recommended minimum configuration:
#
acl manager proto cache_object
acl localhost src 127.0.0.1/32
acl to_localhost dst 127.0.0.0/8 0.0.0.0/32
# Example rule allowing access from your local networks.
# Adapt to list your (internal) IP networks from where browsing
# should be allowed
#acl localnet src 10.0.0.0/8 # RFC1918 possible internal network
acl visitante src 172.16.108.0/24 # RFC1918 possible internal network
acl localnet src 192.168.108.0/24 # RFC1918 possible internal network
#acl localnet src fc00::/7 # RFC 4193 local private network range
#acl localnet src fe80::/10 # RFC 4291 link-local (directly plugged) machines
acl SSL_ports port 443
acl SSL_ports port 4070 # Spotify
acl Safe_ports port 80 # http
acl Safe_ports port 21 # ftp
acl Safe_ports port 443 563 2083 2707 2087 # https
acl Safe_ports port 70 # gopher
acl Safe_ports port 210 # wais
acl Safe_ports port 1025-65535 # unregistered ports
acl Safe_ports port 280 # http-mgmt
acl Safe_ports port 488 # gss-http
acl Safe_ports port 591 # filemaker
acl Safe_ports port 777 # multiling httpa
acl Safe_ports port 69 # Spotify
acl Safe_ports port 78 # Spotify
acl Safe_ports port 4070 # spotify
acl CONNECT method CONNECT
acl SSL method CONNECT
acl whitelist_regex url_regex "/etc/squid/whitelist_regex"
#acl dominios_liberados dstdomain "/etc/squid/dominios_liberados"
#Alterado 05052017
acl palavras_proibidas_visitantes url_regex "/etc/squid/palavras_proibidas_visitantes"
acl palavras_proibidas url_regex "/etc/squid/palavras_proibidas"
acl
[*****] dstdomain "/etc/squid/blacklists/
[*****]/domains"
#
# Recommended minimum Access Permission configuration:
#
# Only allow cachemgr access from localhost
http_access allow manager localhost
http_access deny manager
# Deny requests to certain unsafe ports
http_access deny !Safe_ports
# Deny CONNECT to other than secure SSL ports
http_access deny CONNECT !SSL_ports
# We strongly recommend the following be uncommented to protect innocent
# web applications running on the proxy server who think the only
# one who can access services on "localhost" is a local user
#http_access deny to_localhost
#
# INSERT YOUR OWN RULE(S) HERE TO ALLOW ACCESS FROM YOUR CLIENTS
#
# Example rule allowing access from your local networks.
# Adapt localnet in the ACL section to list your (internal) IP networks
# from where browsing should be allowed
http_access deny
[*****]
http_access allow localnet whitelist_regex
#http_access allow localnet dominios_liberados
http_access deny localnet palavras_proibidas
#Alterado 05052017
http_access deny visitante palavras_proibidas_visitantes
http_access allow visitante
http_access allow localnet
http_access allow localhost
# And finally deny all other access to this proxy
http_access deny all
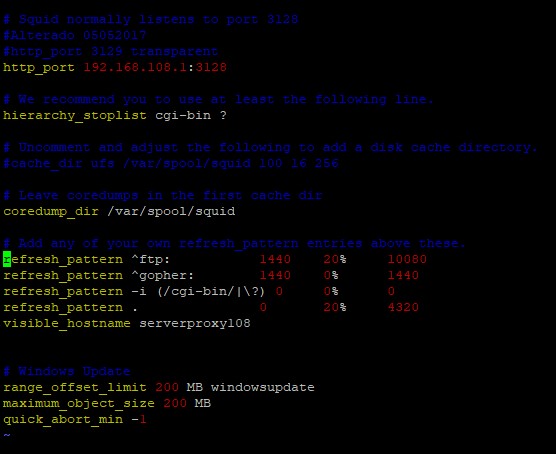
# Squid normally listens to port 3128
#Alterado 05052017
#http_port 3129 transparent
http_port 192.168.108.1:3128
# We recommend you to use at least the following line.
hierarchy_stoplist cgi-bin ?
# Uncomment and adjust the following to add a disk cache directory.
#cache_dir ufs /var/spool/squid 100 16 256
# Leave coredumps in the first cache dir
coredump_dir /var/spool/squid
# Add any of your own refresh_pattern entries above these.
refresh_pattern ^ftp: 1440 20% 10080
refresh_pattern ^gopher: 1440 0% 1440
refresh_pattern -i (/cgi-bin/|\?) 0 0% 0
refresh_pattern . 0 20% 4320
visible_hostname serverproxy108
# Windows Update
range_offset_limit 200 MB windowsupdate
maximum_object_size 200 MB
quick_abort_min -1